Welcome to part three. If you missed part 1, Initial installation and configuration you can see it here. The second part setting up users and domains is here
In part three we will be setting up
- Securing Web Based Email
- Anti-Spam/Virus Measures
- Grey Listing
Configuring router
If you are testing this out in a setup similar to my Test Networking Lab then you will need to forward the ports use by IMAP, POP3, and SMTP.
At the end of my Test Networking Lab post is an example script to setup iptables rules to forward port 80, use it to create rules for ports 25, 110, 143, 993, 995, so they are passed on to the Zentyal server.
You will also want to set up an MX record on your local LAN DNS server to point at the external NIC on your lab-router.
with dnsmasq add a line similar to the following:
mx-host=dragon.lab,lab-router1.dragon.lab,50
Configuring Email
You will need to install the Mail service and the Webmail service from Software Components -> Zentyal Components. After installing them they need to be turned on by clicking the Module Status options icon and then ticking the services you want to start up.
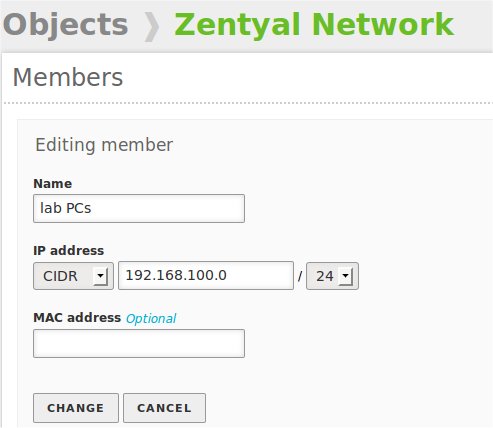
Create a Network object to include all PC’s on the Zentyal side of the lab network that is with an IP address in the range 192.168.100.0/24. We will use it to allow all those PC’s to relay their emails to the Zentyal Mail server.
Find your way over to Network -> Objects, Add a new object as shown below.
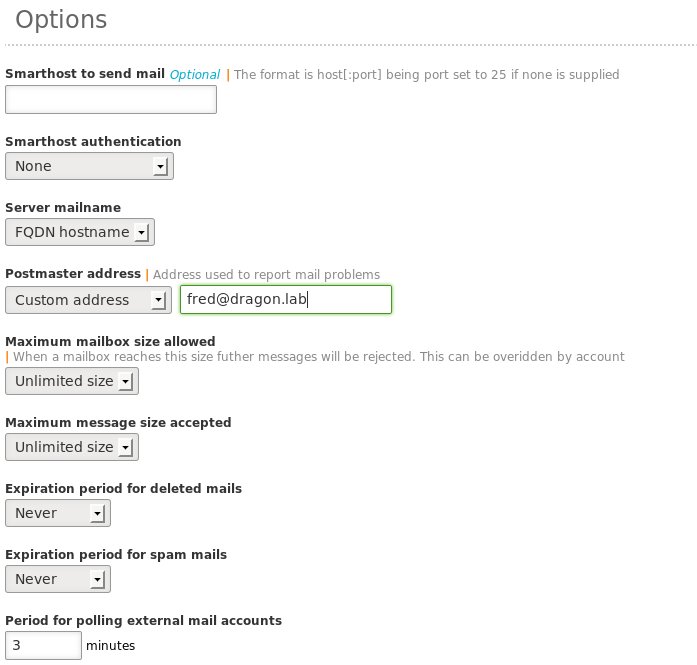
Make your way to Mail -> General -> Mail Server Options -> Options.
I change the Postmaster address, change it to Custom address with an email address pointing to fred@dragon.lab. That is the address I will use during testing. Other than that I used the defaults for these to start with. Then refine them as I need to once it is working. Remember to set that up in the user settings for Fred ‘the admin’ which was done in part two.
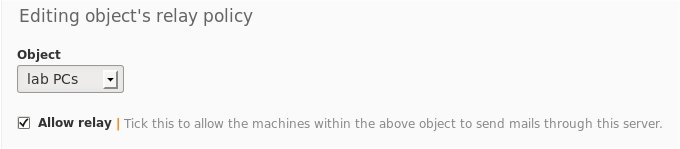
Go to the top tab, Relay policy for network objects, and add the lab PC’s object. Make sure the Allow relay box is ticked. This will allow all lab PC’s to relay email through Zentyal.
You should be able to start the webmail web access with https://localhost/webmail and then login to an account. Fred would be a good choice for now.
Note: The login name is in the format 'username@domain'. So using the test user, Fred 'the admin', as an example the user name will be fred@dragon.lab.
Try sending and replying to emails from the three uses we set up, Fred, Mary and Bert.
What we have is a working webmail service but not a secure one 🙁 We should really secure it by using HTTPS web connections that are forced and only use MAPI+ and POP3s protocols. With web mail we could just use MAPI+. If you have clients using a traditional email client like Thunderbird or Evolution you may want to keep the POP3. It will be simpler than reconfiguring the existing mail clients for all your users.
Securing Web Based Email
To secure Web Based email we need to secure the connection between the browser and the web server. This is best done by using HTTPS connections.
We need to create a new domain, sub domain actually. So pop over to DNS -> then down to the Domains table. Click on the Add New. This opens a new Window. Enter the sub domain name for your email service, I’m using lab-email.dragon.lab.
Save the changes.
You should now be able to ping lab-email.dragon.lab and it will return the IP address of your Zentyal server, in my case it will be 192.168.100.1.
Head on over to Web Server -> Virtual hosts create one called lab-email.dragon.lab, make sure you tick the box for Force SSL and that the Enable tick box is ticked.
Save the changes.
Create the Virtual Domain for your email service, Mail -> Virtual Domains -> Add new virtual domain, call it lab-email.dragon.lab.
Save the changes.
You and your users will now be able to connect into their web based emmail over a HTTPS connection. HTTP will no longer work, which is what we wanted. Try sending some more emails to and from the three test users.
Securing Email
If you are also going to be supporting traditional email clients. We will need those to talk over a secure connection, too. Communications -> Mail -> General -> Mail retrieval services. untick the non-secure options for POP3 and IMAP, if you are planning on only supporting webmail then POP3S can get unticked too. Well, actually if you are planning on only running web based email then this will make little difference as the web server and the mail server are on the same machine, so encrypting their conversations will make little difference from a security point of view. BUT it won’t be of any harm either 🙂
Anti-Spam/Virus Measures
Scroll down to Mail Filter -> SMTP Filter -> General tab. You should find that both the anti-spam and anti-virus boxes are ticked. If for some reason they are not, best tick them, :-).
Under the Filter Polices tab, the defaults are pretty good too, although I also silently drop banned files.
Mail Filter -> Antispam. I add a tag of [SPAM] to the email subject to warn users it may be spam.
Save the changes.
You may want to go down to the Attached files options. I am not going to say what I use here, the flame wars always start over these lists 🙂 Just do what you think is best, you are the Sys Admin after all.
GreyListing
Greylisting is one of the best ways, if the THE best, to stop spam! It works in a really simple way. Your server receives an email from someone. This is checked against a database, keyed with sender IP, From name and recipient name. If a record is not found a polite rejection message is returned saying please try a little later. Well behaved mail server will do so without a problem. Scum of the earth spammers rarely resend their rubbish. 90% of the spam is now stopped before it even gets to your server. After the database check has been done and passed, the emails from that server and From address will simply be passed on to the recipient without further delay.
Mail -> Greylist. Just tick the enabled box and save the changes.